Zero Token Architecture
Zero Token Architecture is nilbox's innovative core security technology. It fundamentally prevents token leakage by never giving the real token to the AI Agent.
Instead of asking "How do we protect the token?", we ask "What if we never give it in the first place?"
The Limits of Traditional Security
Until now, most security approaches have focused on preventing leakage after the token has already been given to the Agent.
- Isolating the runtime environment with Docker or a Sandbox
- Controlling file system/network permissions
- Logging and monitoring access to sensitive information
However, once the token is handed over, risk remains.
- Prompt Injection can cause the Agent to output the token directly
- Malicious packages or hacker programs collect environment variables and send them externally
- The very structure of allowing Agents to execute arbitrary commands creates a leakage path
Perfect prevention is practically impossible.
Nilbox's Paradigm Shift
If there's a risk of leakage, don't give it in the first place.
- A fake token is passed to the AI Agent.
- The real token exists only inside nilbox, where the Agent can never see it.
- The Agent believes the value it received is real, makes calls, and receives normal responses.
How Can You Call an API Without a Token?
Without a token, API calls simply don't work. Nilbox solves exactly that problem.
Before: Traditional Approach
# AI Agent environment variable
OPEN_API_TOKEN=1234
The real token 1234 is directly exposed to the Agent. Even if you use Docker or a Sandbox, you still have to pass it at some point.
After: nilbox Zero Token Approach
# AI Agent environment variable
OPEN_API_TOKEN=OPEN_API_TOKEN
The token is passed following the rule where the token name and value are identical. The Agent treats the string OPEN_API_TOKEN as a real token.
Substitution Flow
The moment the Agent makes an API call, nilbox intercepts the request and substitutes the real token.
- AI Agent — Calls the LLM with
Authorization: Bearer OPEN_API_TOKEN - nilbox — Intercepts the request and substitutes
OPEN_API_TOKEN→1234 - LLM server — Responds normally with the valid token
1234 - AI Agent — Receives the normal response, convinced that its token is real
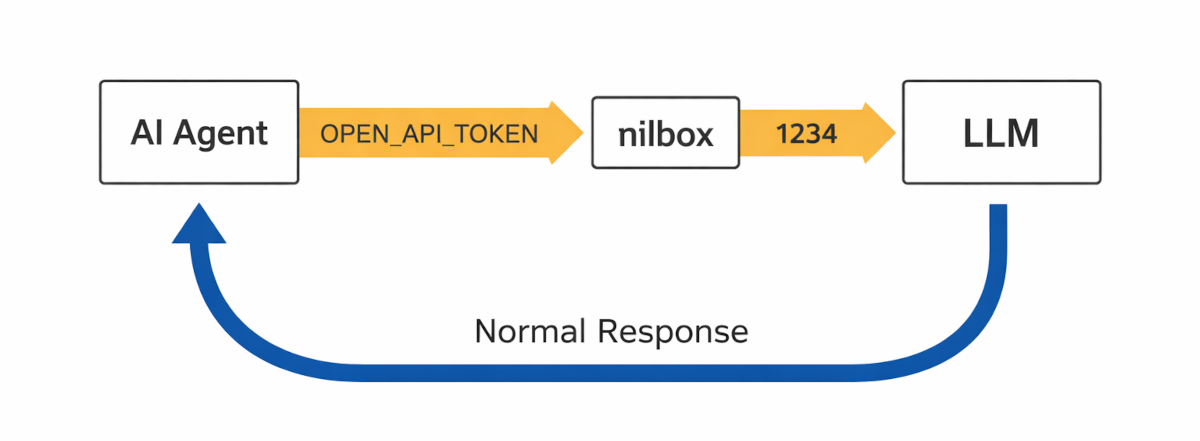
The AI Agent is completely unaware of nilbox's existence.
Hacker Scenario: Why It's Safe Even If Leaked
Imagine a hacker program is installed on the system and leaks the token via email.
- Traditional approach:
OPEN_API_TOKEN=1234leaks as-is → critical - nilbox approach:
OPEN_API_TOKEN=OPEN_API_TOKENleaks → a meaningless string
We don't try to prevent leakage. We hand over a value that is useless even if leaked. What ends up in the hacker's hands is just a plain name string — they cannot call the LLM.
Summary
- Zero Token Architecture is a security architecture that never gives the real token to the AI Agent.
- A fake token in the form
KEY=KEYis passed to the Agent. - nilbox substitutes the real token at call time and passes it to the LLM.
- Even if a leak occurs, the value that goes out is a meaningless name string, so the real token is never exposed.